Check out this video from the U.S. Cybersecurity and Infrastructure Security Agency (“CISA”) on four things you can do to stay safe online:

Social engineering is a scam where a cybercriminal attempts to trick someone into taking an action against their own best interests. Usually, the action results in the victim providing confidential information (like their login information) or installing malware on their computer. Most social engineering attacks have four common traits, which signal a far higher likelihood of a scam if all are present.
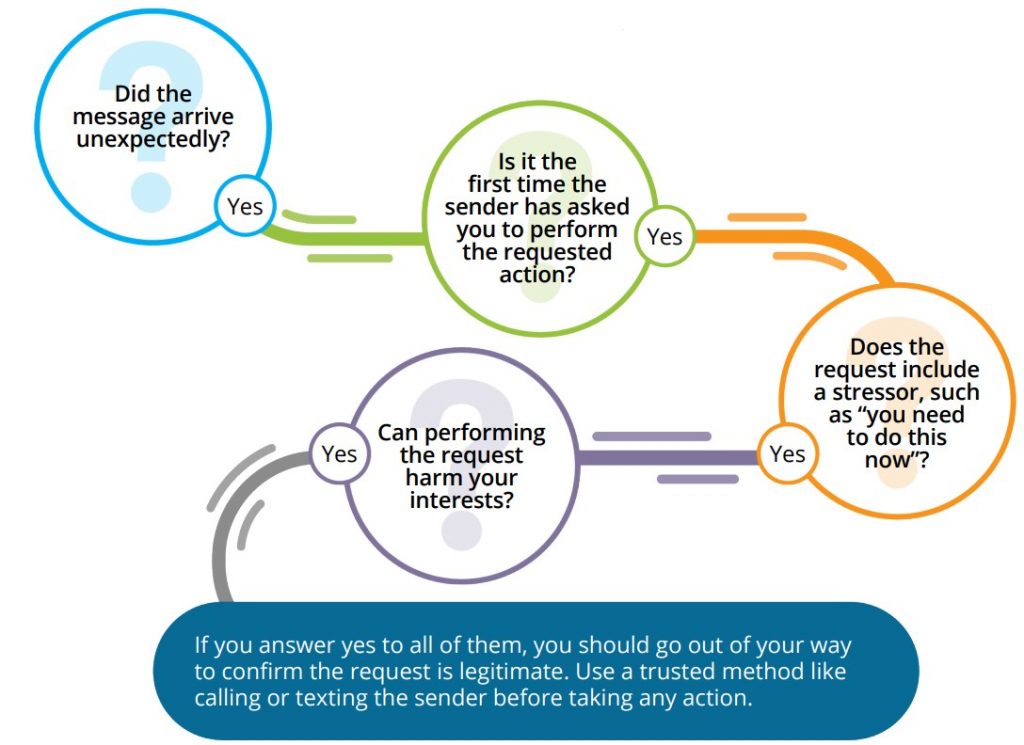
Long Image Description:
Did the message arrive unexpectedly? Yes. Is it the first time the sender has asked you to perform the requested action? Yes. Does the request include a stressor, such as “You need to do this now”? Yes. Can performing the request harm your interest? Yes. If you answer yes to all of them, you should go out of your way to confirm the request is legitimate. Use a trusted method like calling or texting the sender before taking any action.
Not every message with these four traits is absolutely a social engineering scam. Our email inboxes, voicemail and postal mailboxes are full of unexpected requests; that is life. But when these four traits are present, stop, look, and think before you act!
Phishing and social engineering campaigns are still a top source of ransomware and other malware[1].
Phishing is a type of cybersecurity attack where malicious actors send messages pretending to be a trusted person. Social Engineering is the psychological manipulation of people into performing actions like installing malicious software, clicking a malicious link, or divulging sensitive information.
Reduce your chances of your falling victim to phishing attacks!
Beware of messages that:
If an email looks suspicious, do not respond and do not click on any links or attachments. When available, “Report phishing” to block other suspicious emails.
[1] 2023 Verizon Data Breach Investigations Report (DBIR)
Please send any questions or concerns to Simmons Information Security Officer, Kristen Howard, or the Technology Service Desk.
See Yourself in Cyber. #BeCyberSmart.
Even though cybersecurity may seem like a complex subject, ultimately, it’s really all about people. This month we focus on the “people” part of cybersecurity, providing information and resources to help everyone make smarter decisions whether on the job, at home, or at school.
4 Things You Can Do to #BeCyberSmart